How Developers Can Build Agentic Agreement Workflows on Docusign IAM
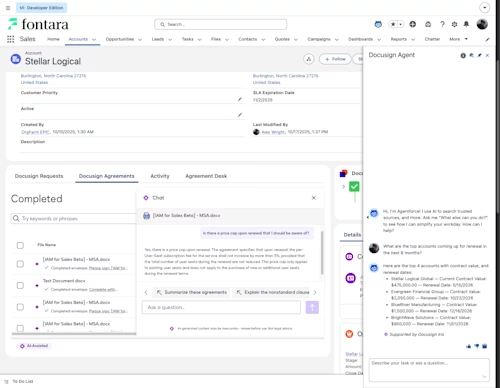
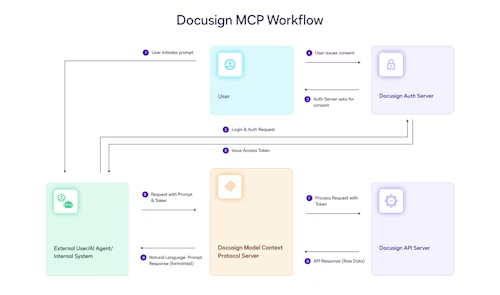
See how the new releases at Docusign Momentum ’26 help builders create agentic agreement workflows, from ingesting agreement data with the Agreement Manager API to exposing tools through MCP and managing integrations in the Developer Console.