Featured topic
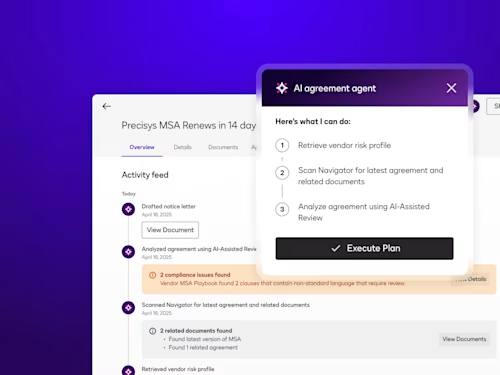
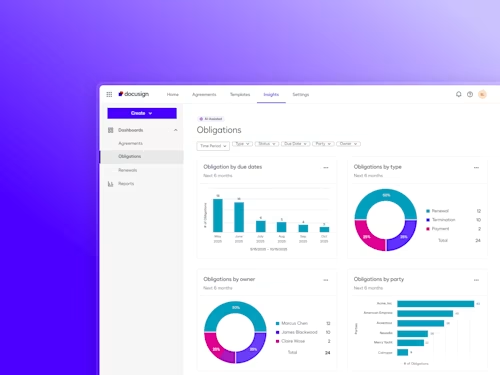
Intelligent Agreement Management
See how Intelligent Agreement Management helps organizations to create, commit to, and manage agreements through a single, streamlined workflow.
Popular posts
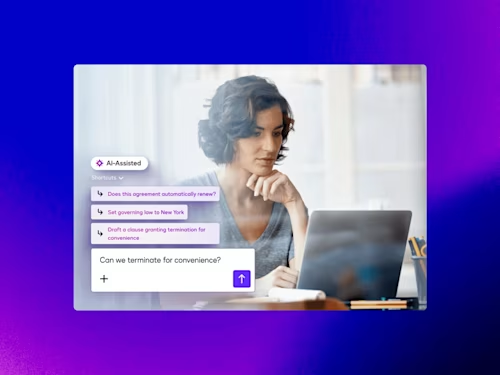
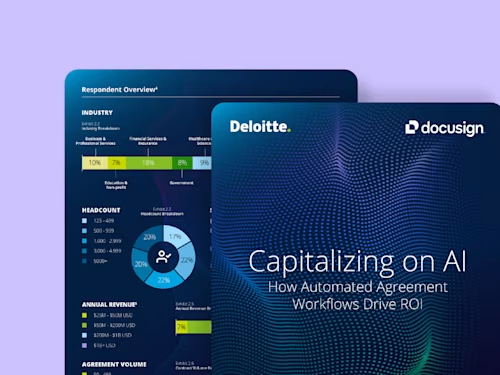
How Contract AI is Transforming Business Workflows
Contract AI helps legal, procurement and sales teams accelerate manual, labor-intensive steps in the contract process and analyze insights in agreement data to inform strategic decisions.

Latest posts
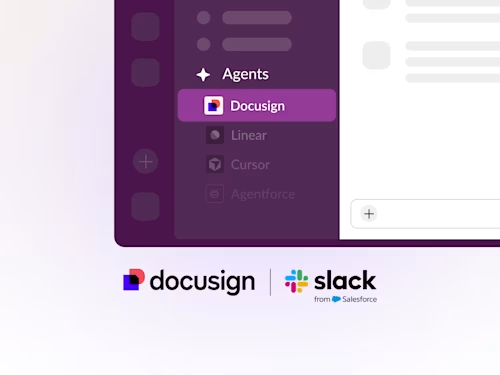
Docusign IAM is the agreement platform your business needs